Election security has been studied for many years by computer scientists, but it is not as often that it attracts so much mainstream attention. I would never have expected to see my former Princeton colleague Andrew Appel on a Sean Hannity segment tweeted by President Trump.

It may seem that even if it has partisan motivations, the recent GOP interest in election security is overall a positive thing. Who wouldn’t want elections to be more secure? Who wouldn’t want less fraud? However, in a very precise sense, the definition of “election security” used by the GOP these days corresponds to election insecurity.
To understand this claim, consider what it means for an election to be secure. (Let’s focus just on the correctness aspect of the count, since it is at the heart of the current issues, and not on the very interesting privacy aspect.) Computer scientists use the technical terms “cast as intended“, “recorded as cast“, and “tallied as recorded“. In other words: if a voter X intends to cast vote for candidate Y, then this vote should be recorded and tallied, and only such votes should be tallied.
With mail-in voting, there are several potential points of failure on the path between voter intent and the final tally:
- Mail can be lost or delayed too much, leading to the vote not counting.
- A third party could intercept the ballot and impersonate the voter.
- A ballot may not be formatted properly in some way, leading to it being disqualified.
- There can be errors or hacks in the tallying process.
Election security is about combatting points 1-4 (of which the last 3 are also applicable to in-person voting) , ideally in a way that is verifiable to the individual voters. Achieving verifiability while maintaining secrecy and not requiring the voter to trust complex technology is a challenging task, but there have been some proposed solutions (see above links).
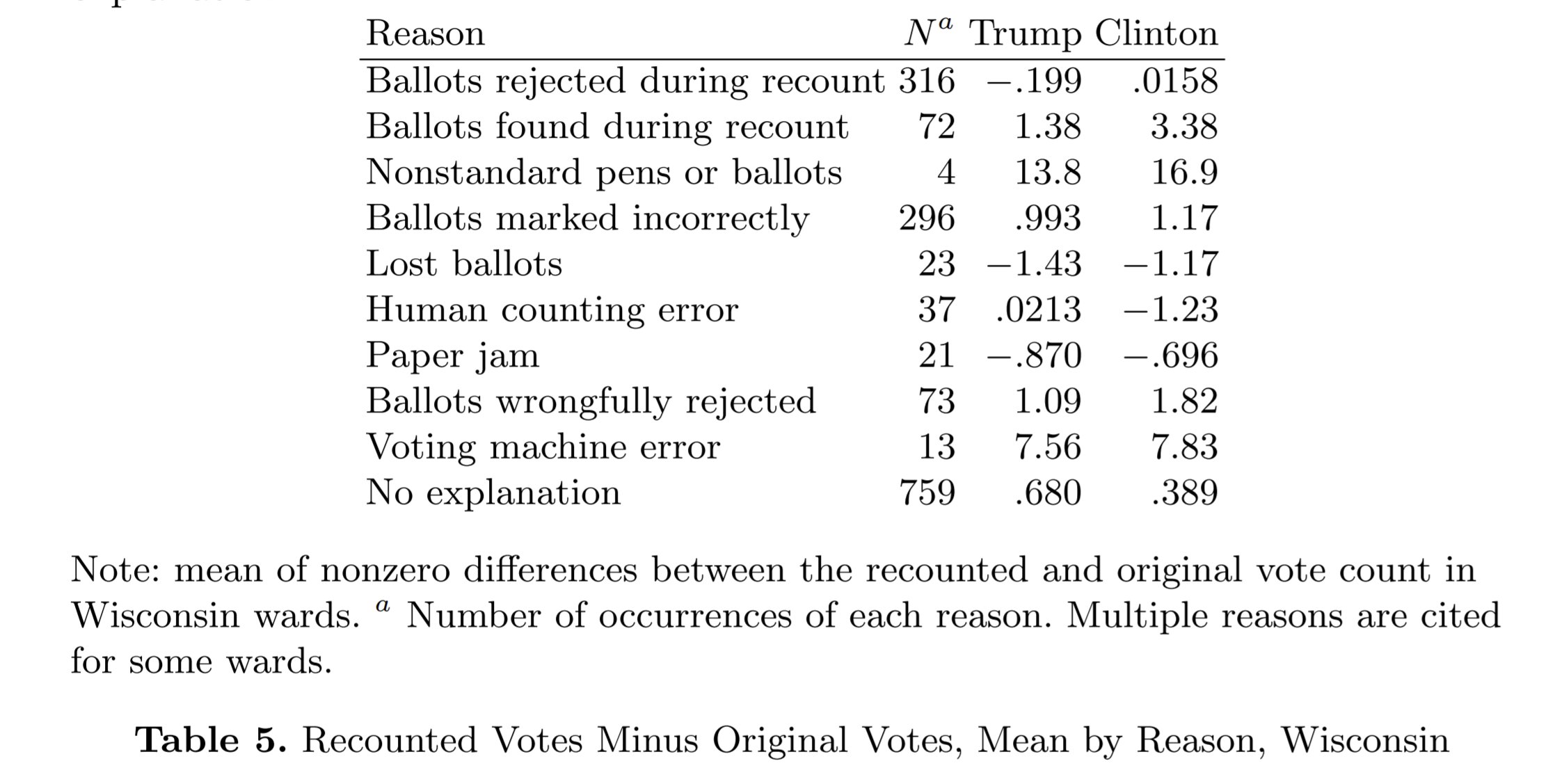
The Hannity segment and much of the “Dominion” non story focused on point 4. This is an important point, but as Appel himself notes, paper ballots, which are mostly used in the US, serve as a way to audit counting. Re-counting is important, and is commonly done, but such recounts often change the total counts by relatively little (and the changes mostly cancel out). For example, here is the list of ballots changed and reasons from the Wisconsin 2016 count (taken from this paper)
In contrast, many of the legal cases by the Trump campaign focused on signature verification and other ballot irregularities. There are two main reasons why a signature would not match between a ballot and driver’s license or other records:
- The signature may have been forged by someone trying to impersonate the voter.
- The voter’s signature might not very consistent, or maybe they have more than one signature (for example, I sometimes sign in Hebrew and sometimes in English) .
Empirically, reason 2 is much more common than reason 1. If a ballot is tossed out because of the second reason it corresponds to a break between the voter intent and the final tally, and hence it is a case of election insecurity. For this reason, making more stringent signature checks could make elections less secure!
While President Trump might claim on Twitter that the election was stolen by a massive conspiracy involving forging of tens of thousands of ballots, this is not the actual content of the court cases (especially after some recent amendments). For example, at the heart of the PA case is the process of “curing a ballot“. This is when a ballot is disqualified due to some technical issue, and a voter has a chance to fix it. Curing a ballot ensures that the voters intent is captured, and hence makes elections more secure.
In PA, the decision of whether to notify voters in such cases was left to the counties, and apparently Democrat-controlled counties were more likely to do so Republican-controlled counties. This is a shame, and had the Trump campaign asked to extend the deadline for curing ballots, then I would think it makes perfect sense. However, this is not what their lawsuit is about. To quote their complaint: “plaintiffs seek a permanent injunction requiring the County Election Boards to invalidate ballots cast by voters who were notified and given an opportunity to cure their invalidly cast mail-in ballot.” This are ballots where there is no question of the eligibility of the voter, nor of the accuracy of their intent, yet the Trump campaign seeks to prevent them from counting. I call this election insecurity.
p.s. See Adam Klasfeld’s feed for more about the various Trump campaign cases
Hm, this is unsettling, and well written.
Nice points! You showed the image of Andrew Appel’s testimony but you didn’t link https://verifiedvoting.org/ founded by computer scientists David Dill, Barbara Simons and others a couple of decades ago to lobby against purely electronic solutions for voting. It includes people like Ron Rivest, Andrew Appel and other computer scientists. The “most-secure election in US history” comment that Krebs made likely can be justified in no small measure due to their lobbying over the years. (Even before electronic voting methods, for years jurisdictions like NYC had mechanical voting machines whose votes could not be audited.)
Thanks Paul! I didn’t know about this! I did know that many of the paper trails and risk auditing recounts that are taking place are due to advocacy by computer scientists and other experts.