This fall, I taught my course CS 127: Cryptography, based on my lecture notes: “An intensive introduction to cryptography”. This is a course that starts with no background knowledge, and gets to advanced concepts including lattice-based (aka “post quantum”) encryption, fully homomorphic encryption, zero-knowledge proofs, multiparty secure computation, software obfuscation, quantum computing and crypto, and more.
As in previous years, I had an fantastic group of students, several of whom produced impressive course projects. These include the following:
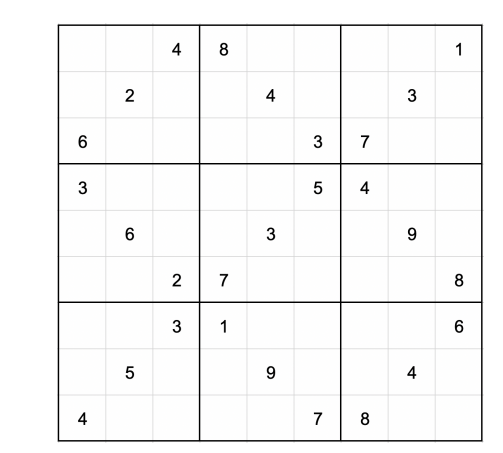
Gavin Uberti, Kevin Luo, Oliver Cheng, and Wittmann Goh implemented Witness Encryption. Witness encryption is a cool concept whereby you can encrypt a secret X (for example the private key corresponding to a bitcoin wallet) so that people can decrypt X if and only if they can find a solution to some puzzle P. You can do this even if you don’t know a solution yourself! So for example you could use this to offer an automatically paying reward for a formal proof of the Reimann Hypothesis, or as they did, offer 2270 Satoshis to anyone solving this Soduko puzzle:
Simas Sakenis wrote a survey of proofs of stake in cryptocurrencies, providing a uniform formalizaiton of proofs of work and proofs of stake, and explaining the difference.
Michael Kiestra and Beatrice Nash proposed CLAMBAKE, a protocol that uses broadcast encryption and Yao’s garbled circuits to achieve a privacy-preserving protocol for facilitating access to controlled resources such as university buildings.
(There were more projects in the course, but some students preferred not to post these publicly since they are still working on them; I will update this post with more projects if appropriate.)
These projects sound awesome, and thank you for posting the lecture notes, they look fantastic. Is there any chance you have recordings of any of the lectures?
Sorry but Harvard doesn’t let us post these online
Why is cryptography relevant in today’s world? On the one hand, isn’t Diffie-Hellman sufficient for practical purposes? On the other hand, it is plausible, that if the american state wants, it can intercept your communication vs backdoors, or simply through cooperation, so to speak, from american IT companies, without cracking any cyphers.
So, apart from being an intellectual exercise, is it still relevant?
Neither is true. First of all, achieving the basic goal of secure point to point communication involves much more than “Diffie Hellman”. There’s a reason why it took decades to understand issues such as the importance of chosen ciphertext security, forward security and more. There is a reason why SSL and TLS have so many version.
Second, crypto is used for more than securing communication and with time more and more advanced crypto is being used. (Not just in cryptocurrencies though that’s of course the most recent example.)
Third, it’s not that easy for governments to get your data if you use cryptography correctly. That’s why they try to pass laws restricting cryptography all the time.